Trending about Digiwonk


how to
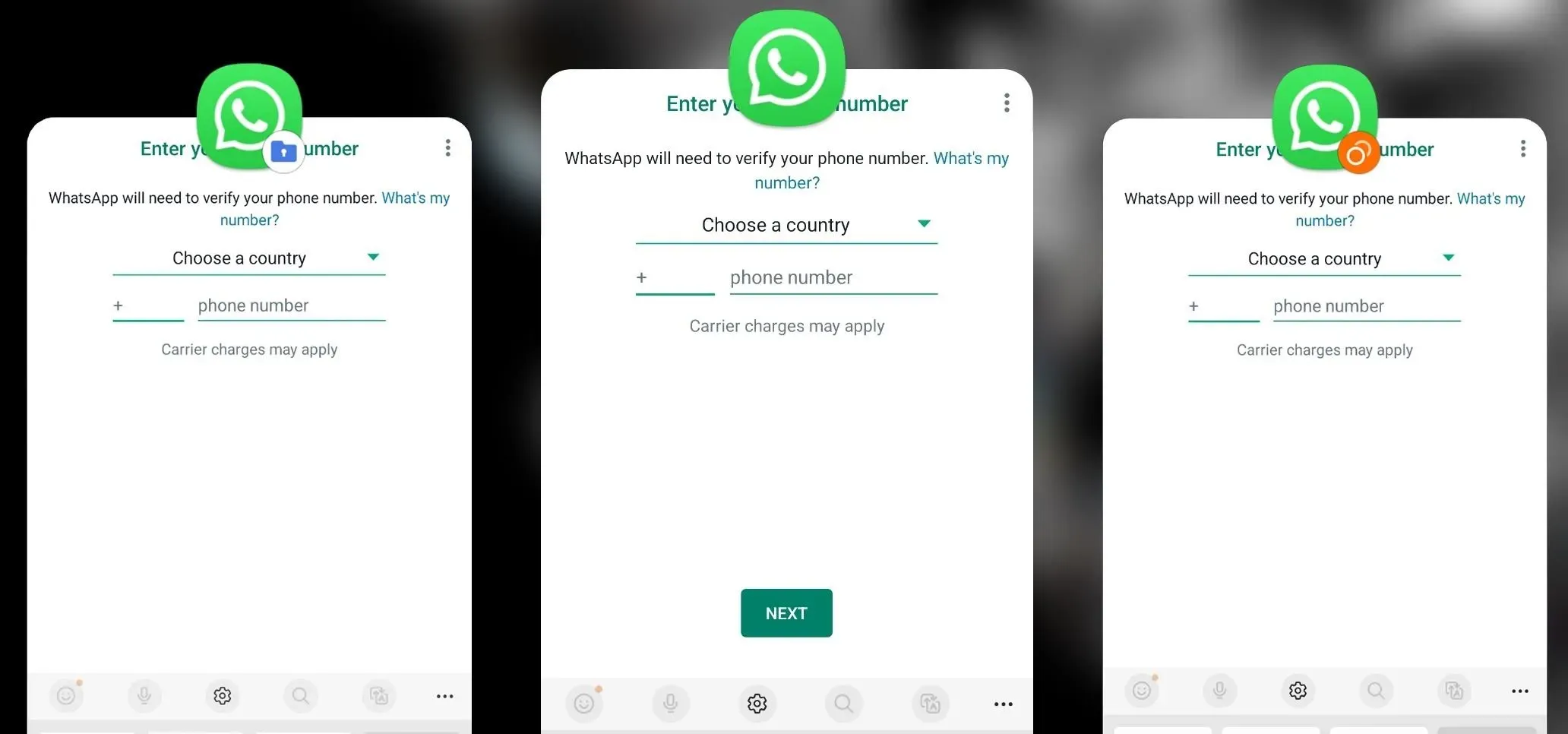
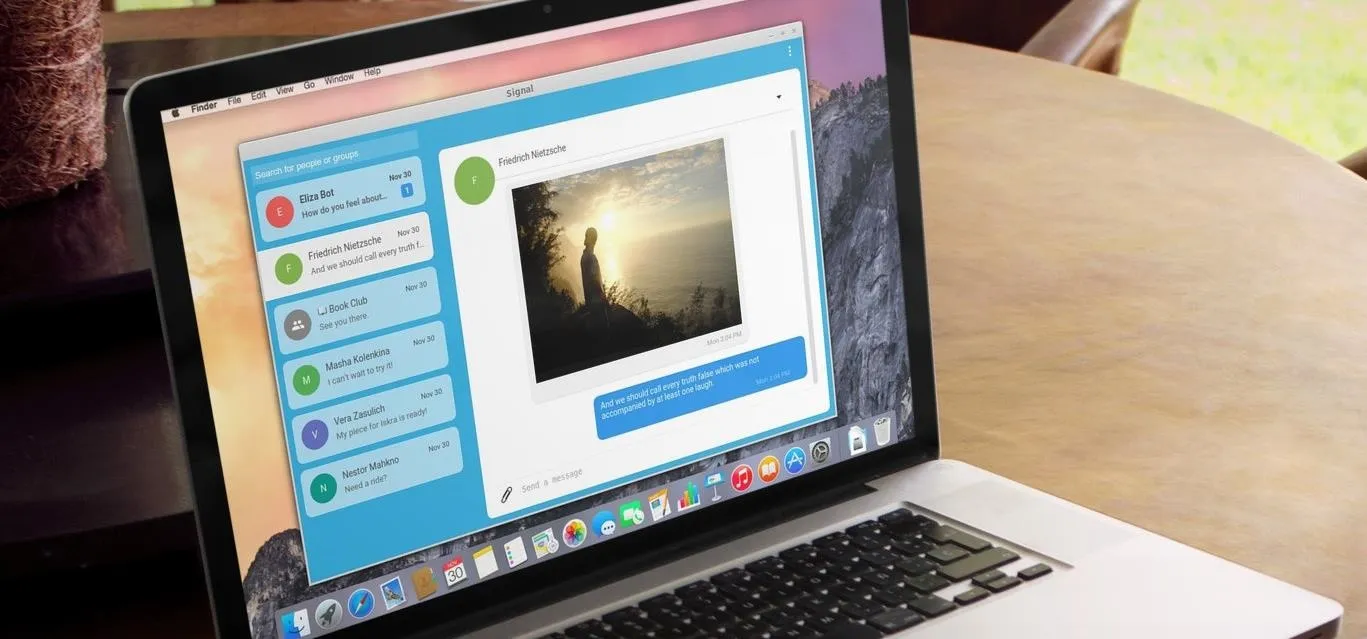
Your One-Stop Guide to Secure, Encrypted Messaging


how to
Apps & Extensions You Should Be Using Right Now in Chrome

how to
Block Spoilers for TV, Movies, & Sports in Your Browser
Featured On Gadget Hacks:
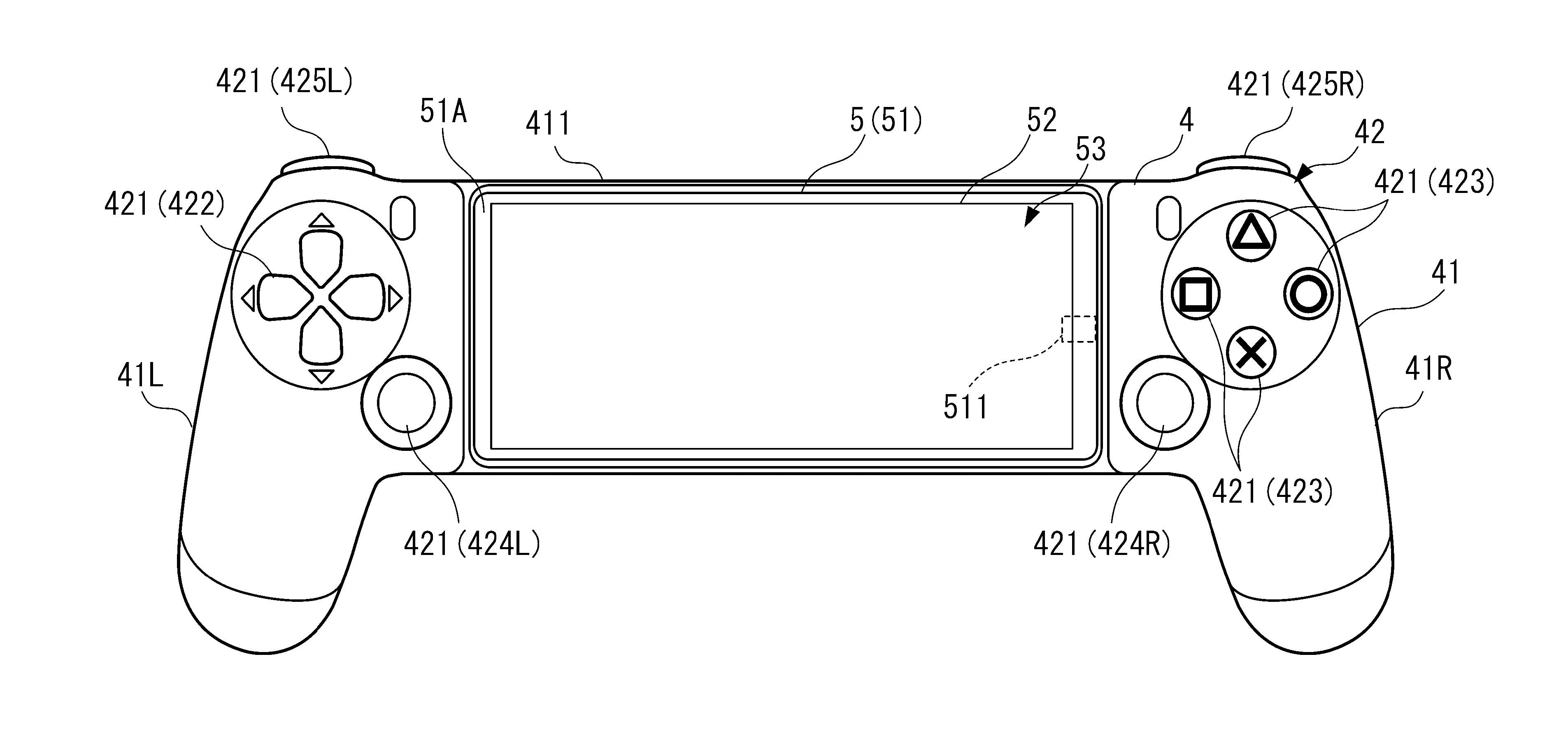
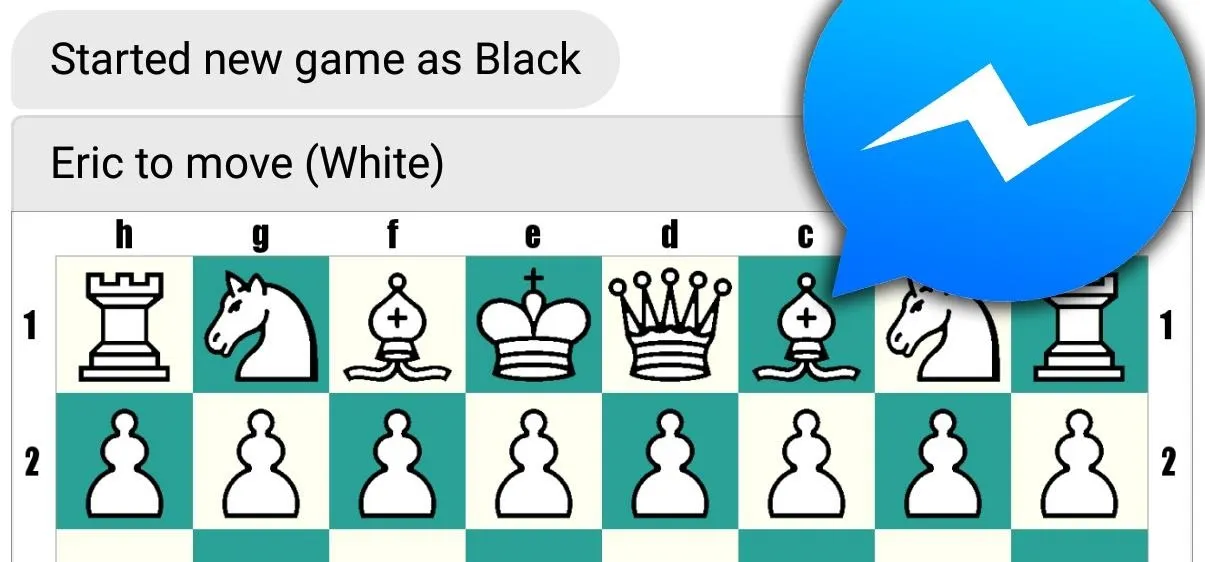
Gaming








Featured On Gadget Hacks:
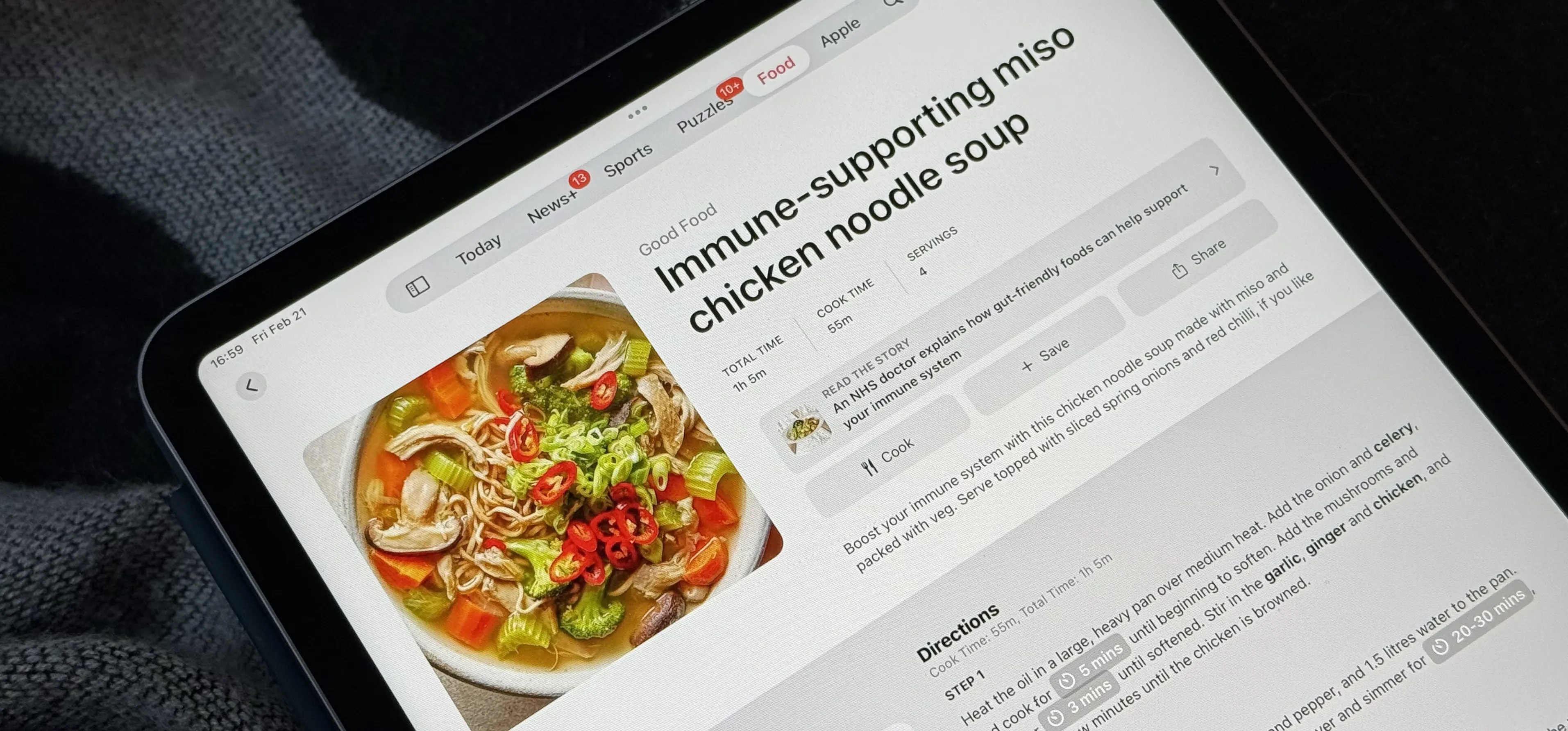
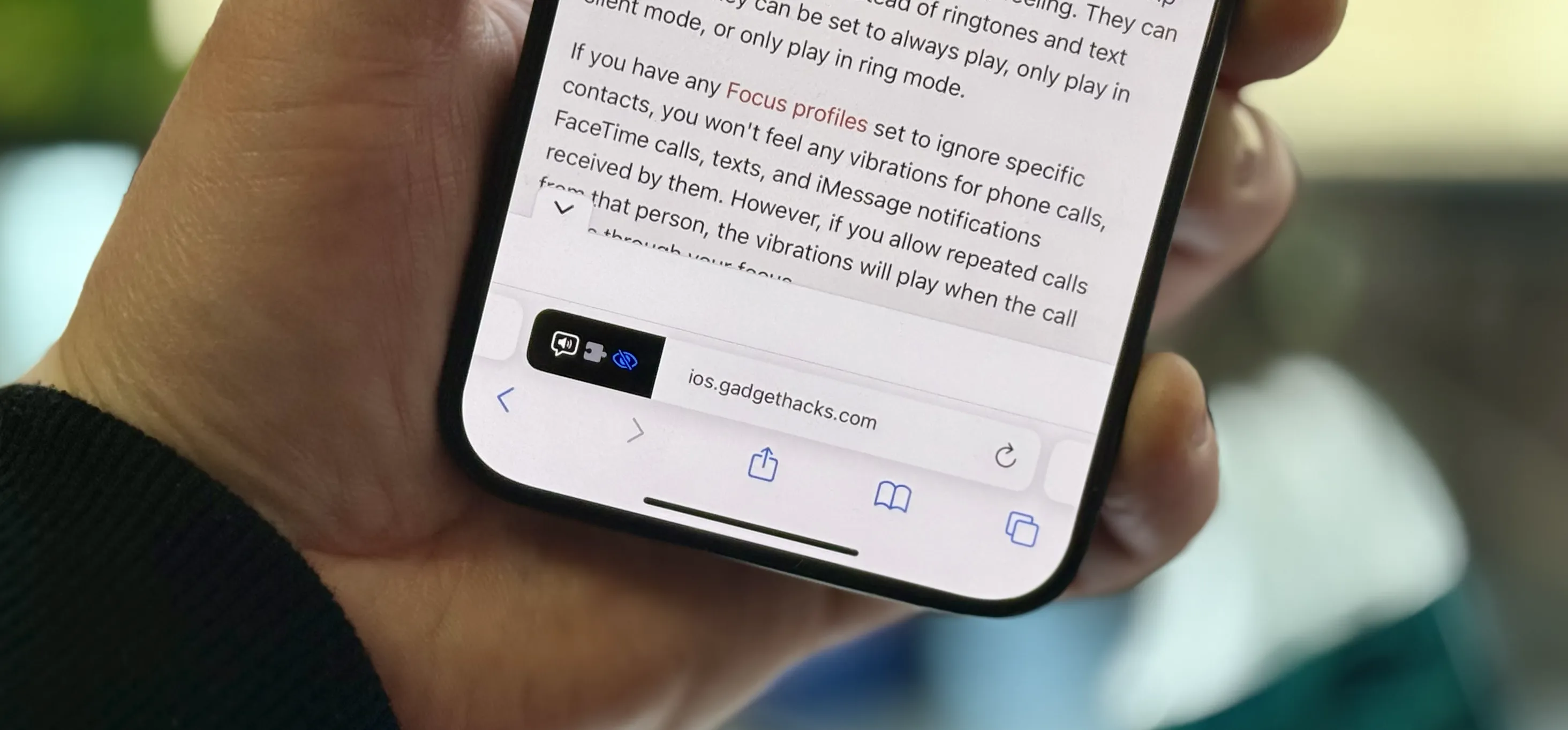
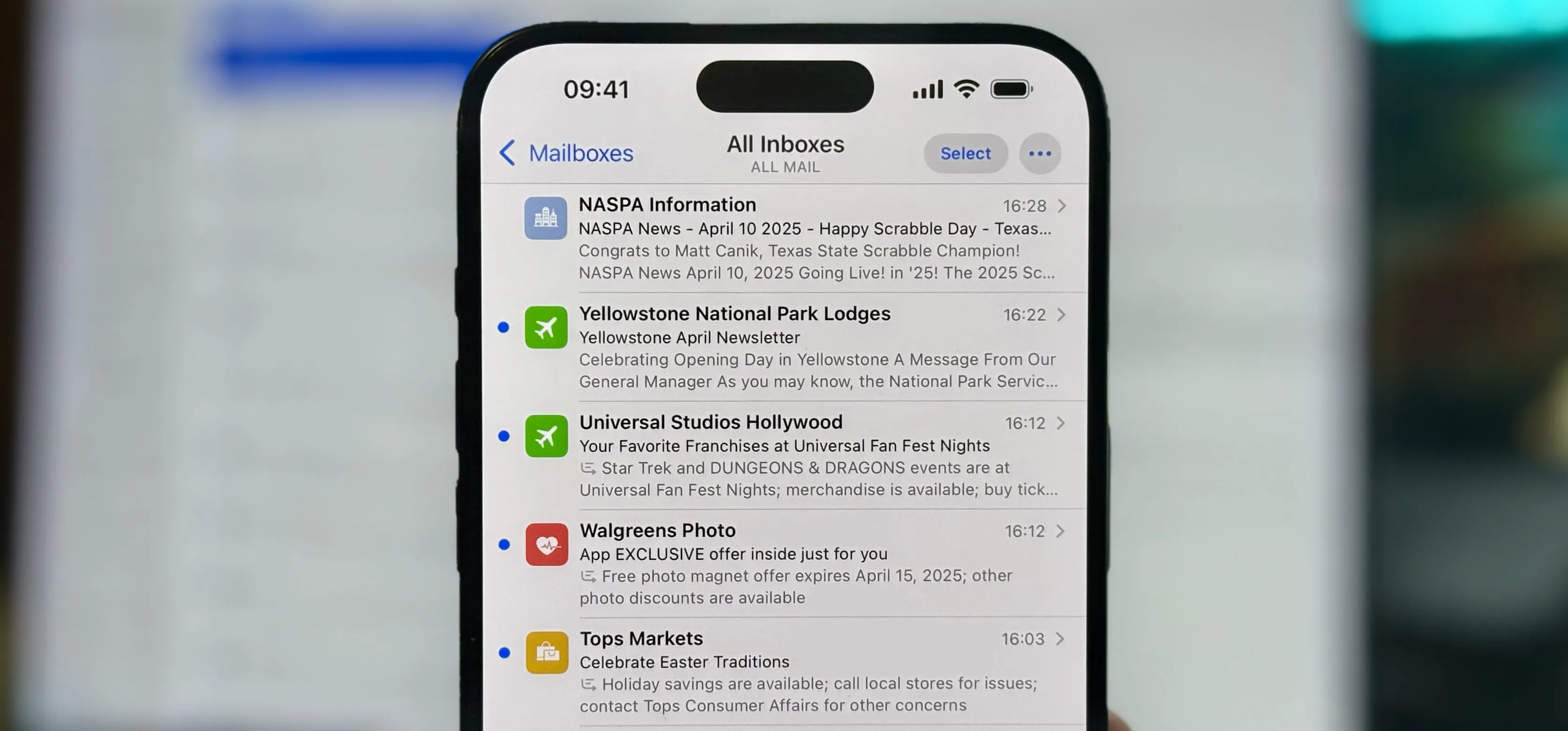
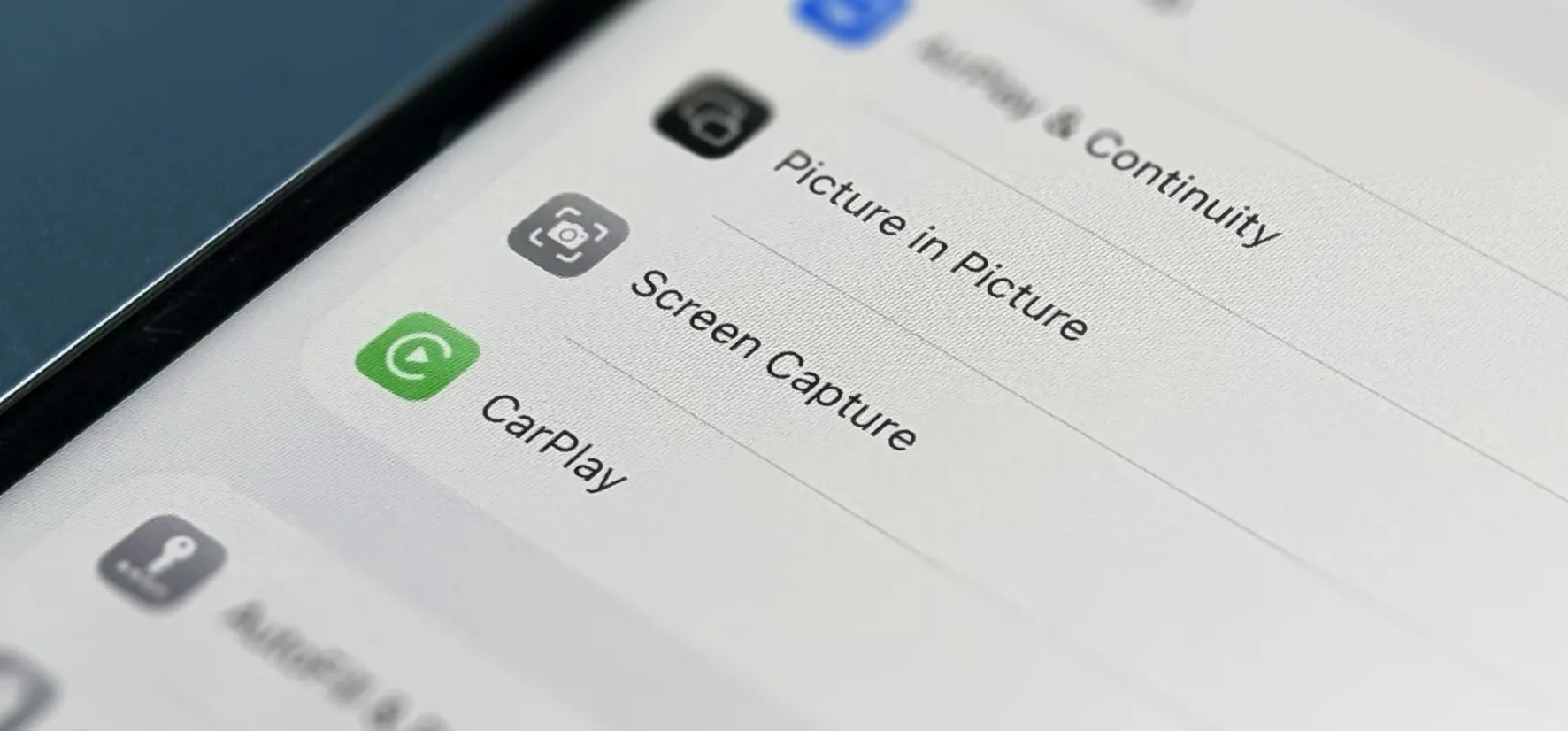
iOS 18


forum
Hi. 



Featured On Gadget Hacks:
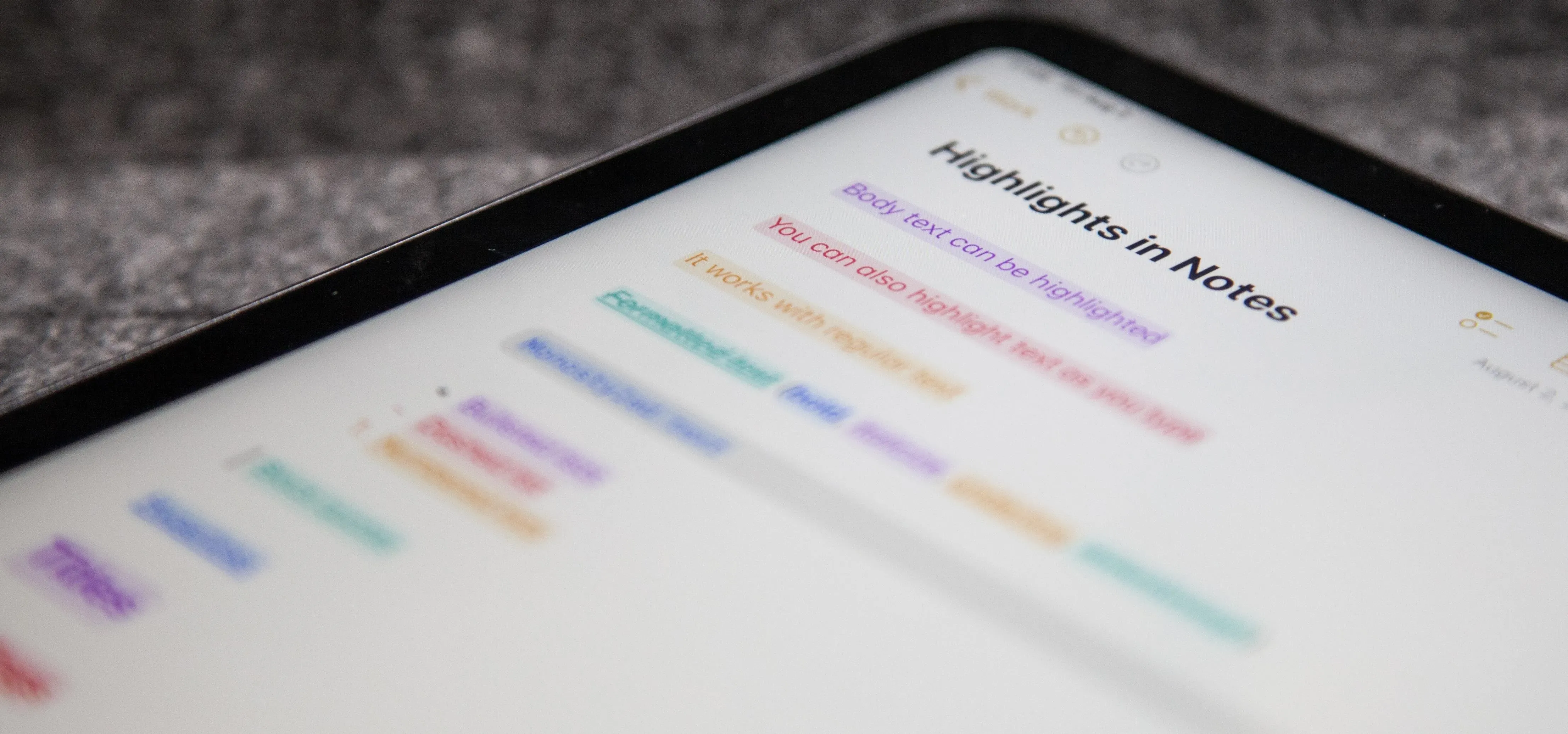
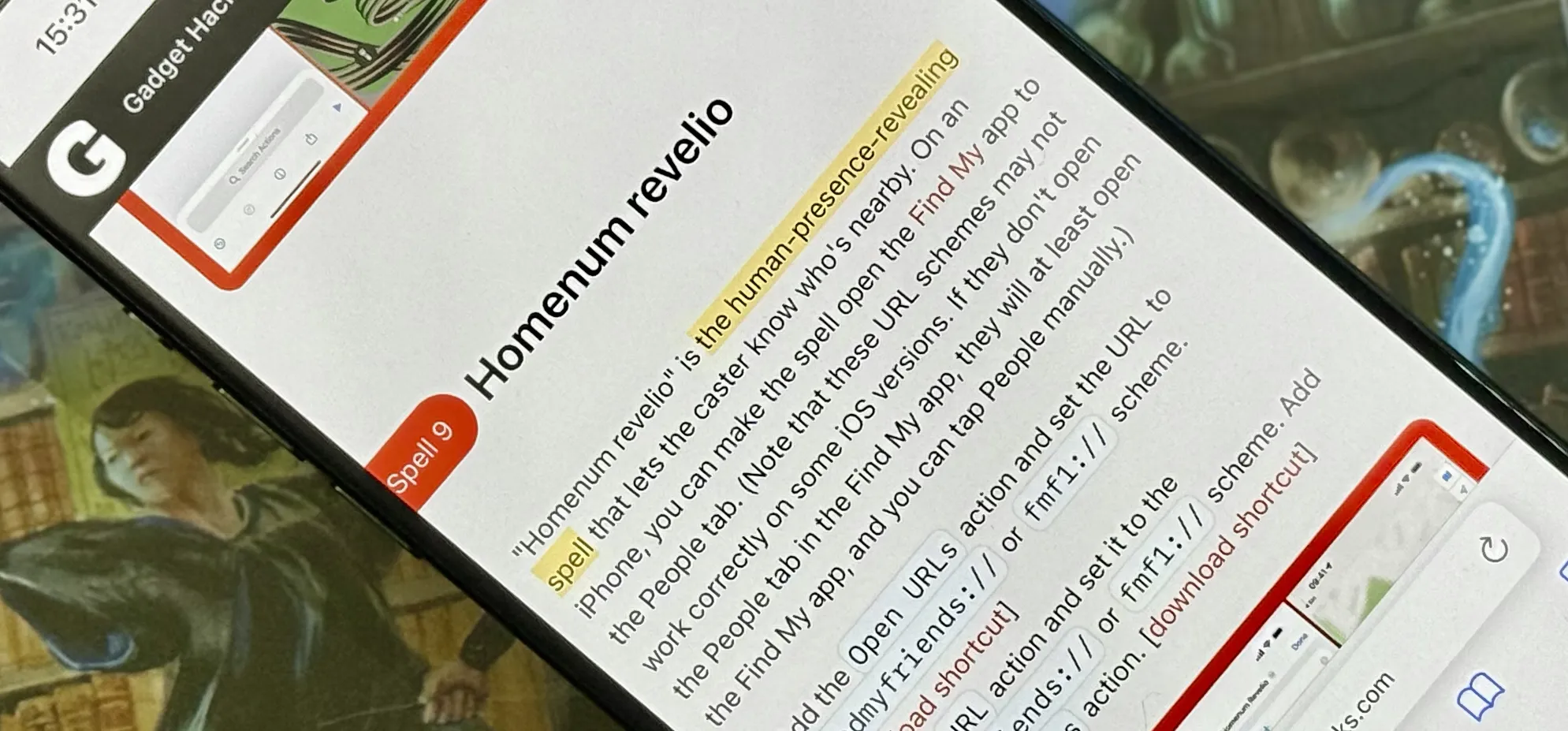
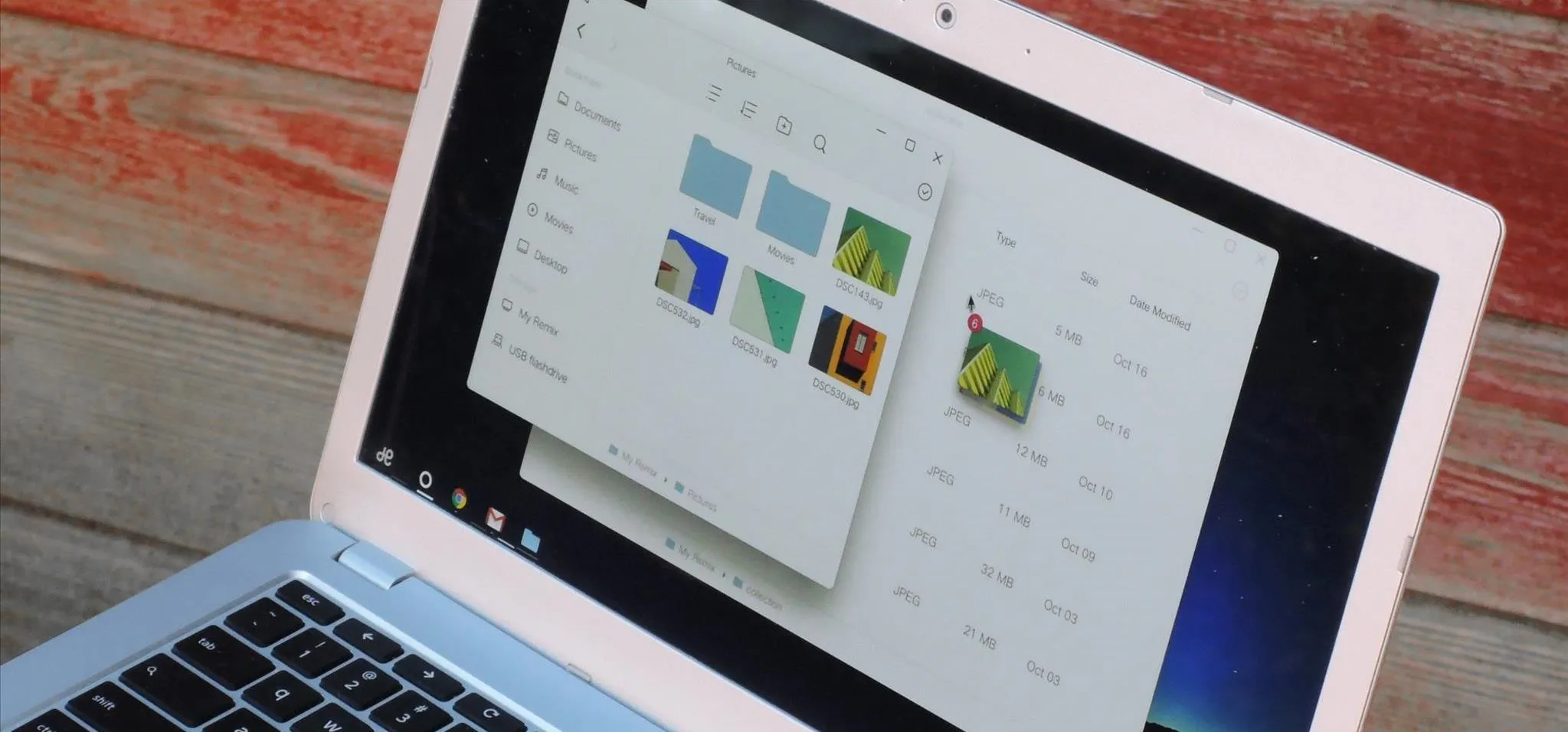
Productivity & Shortcuts









Featured On Gadget Hacks:
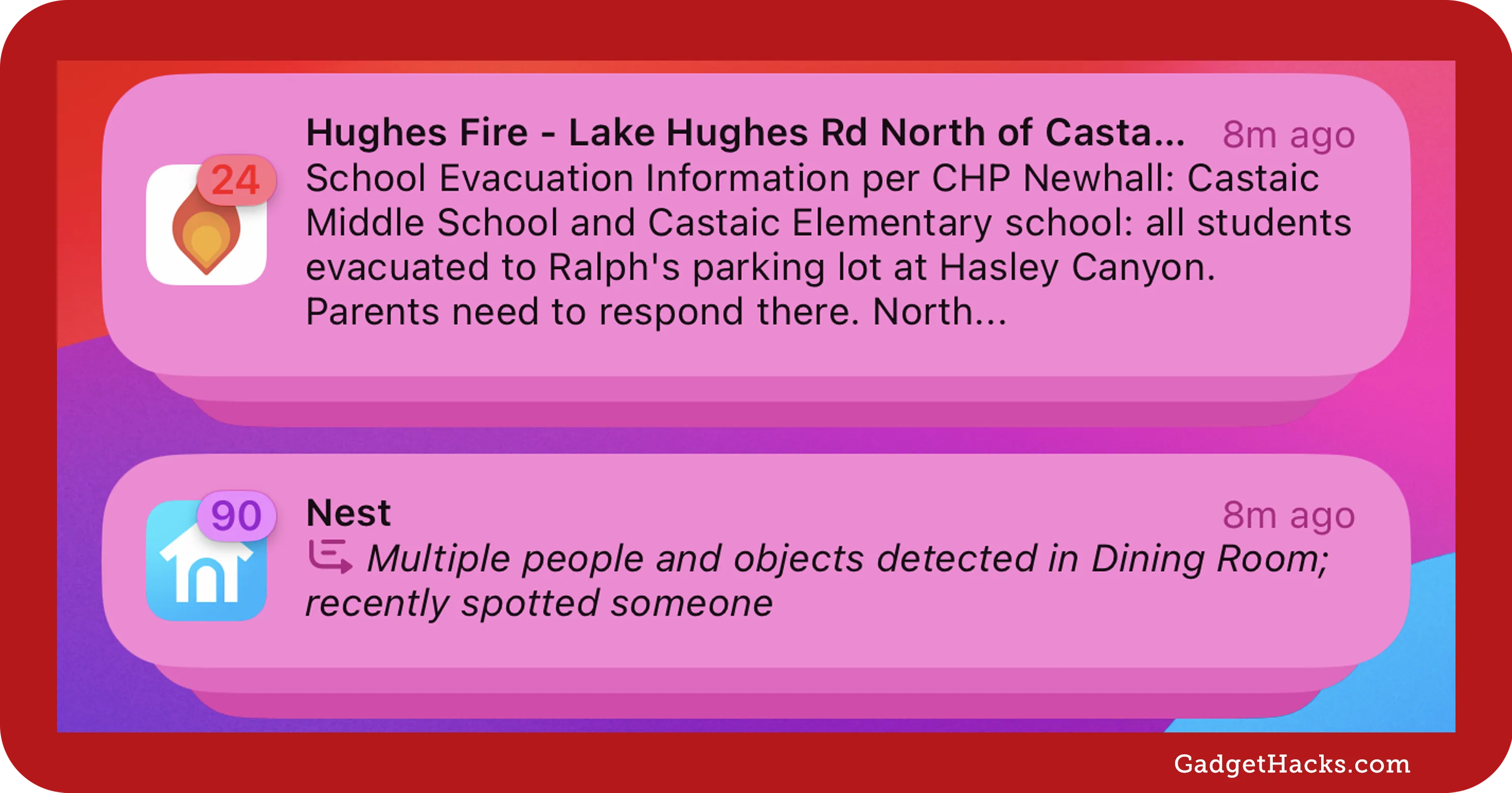
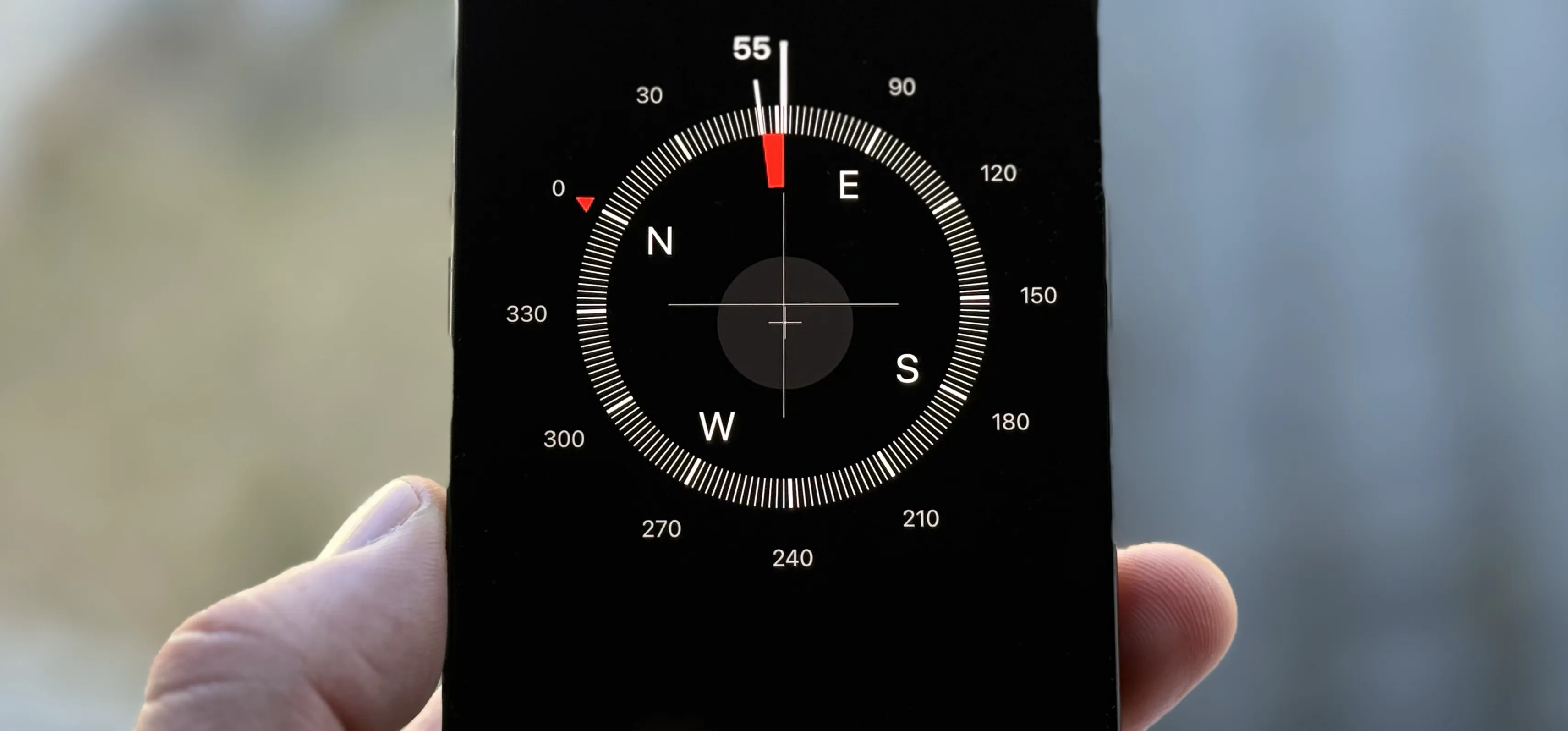
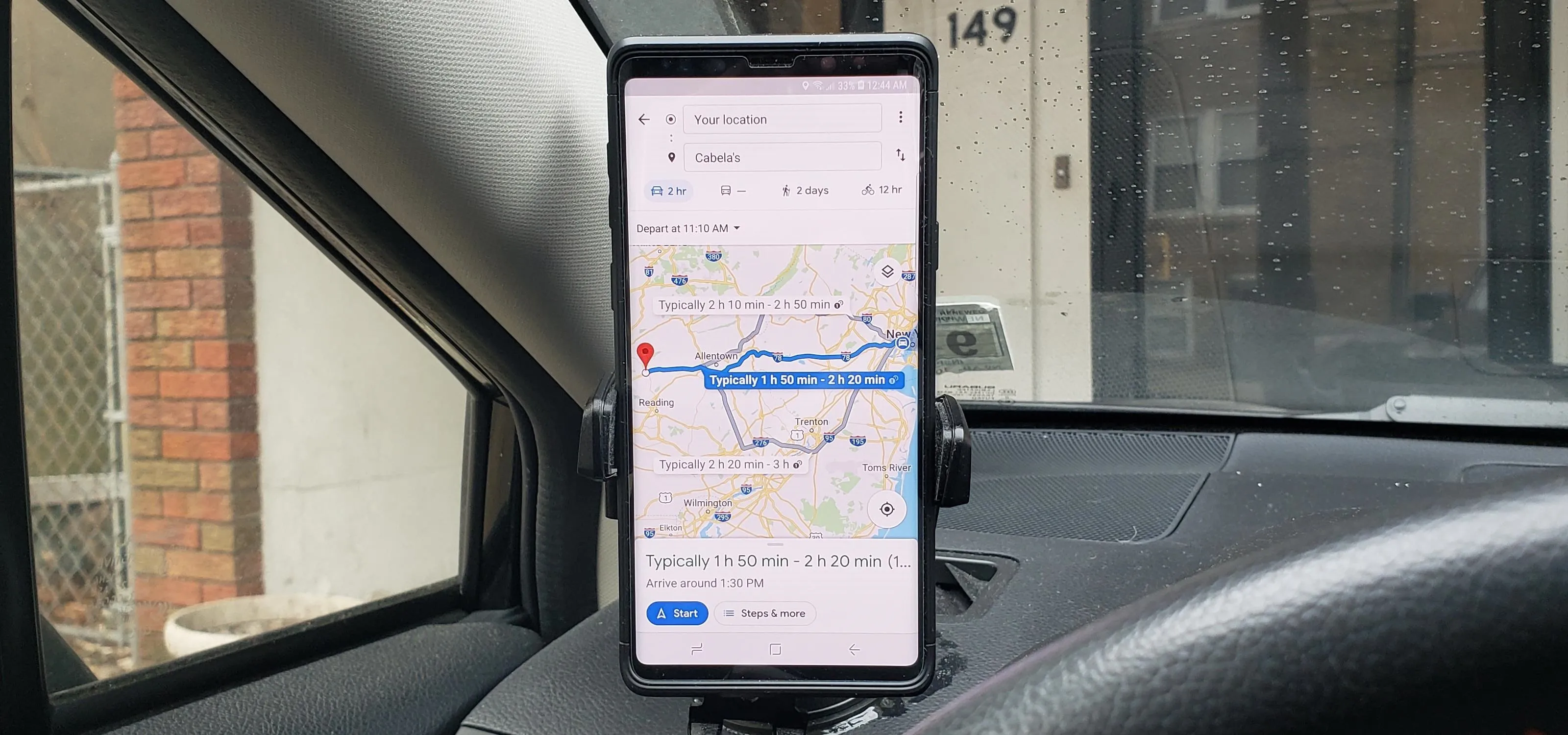
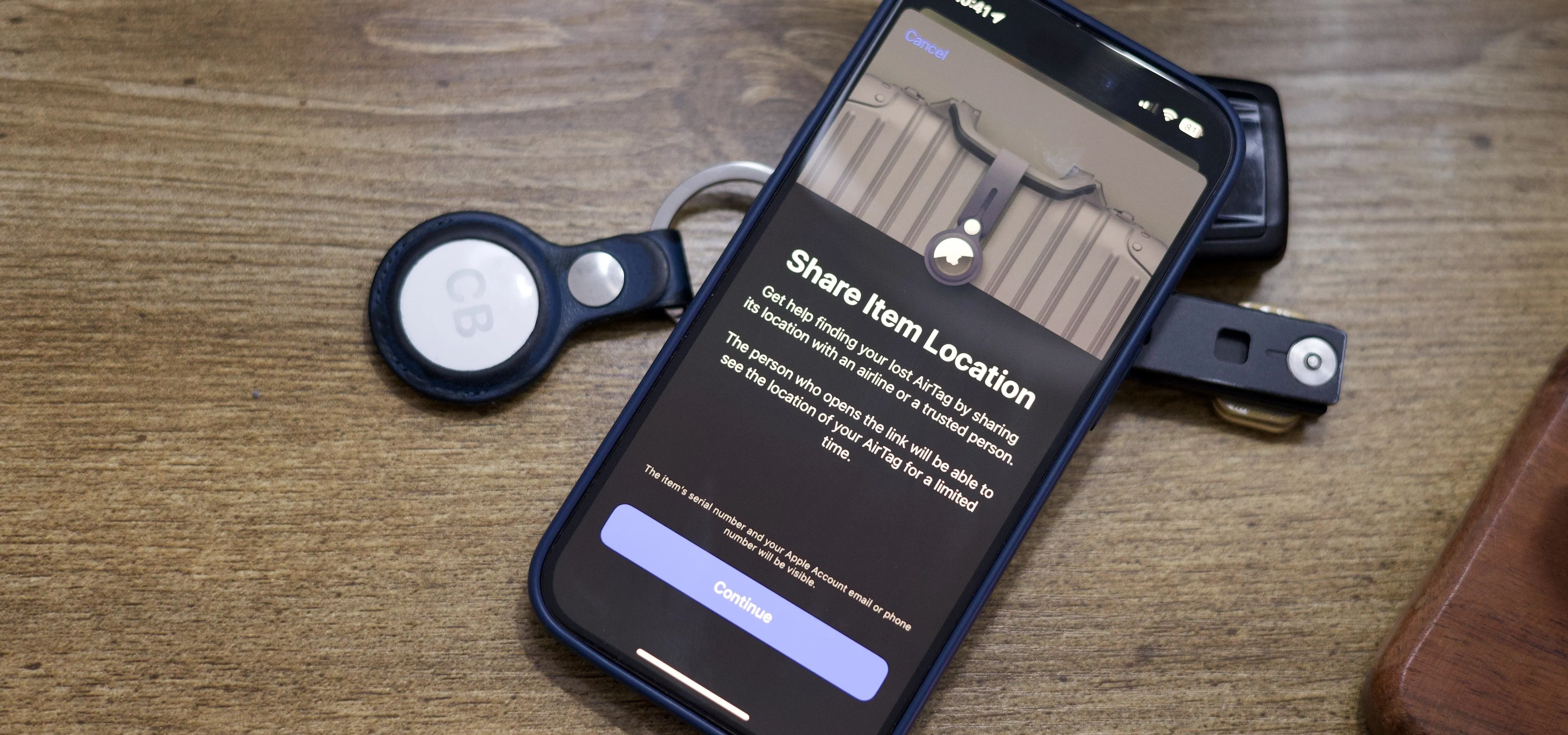
Travel Tips for Your Phone








































how to
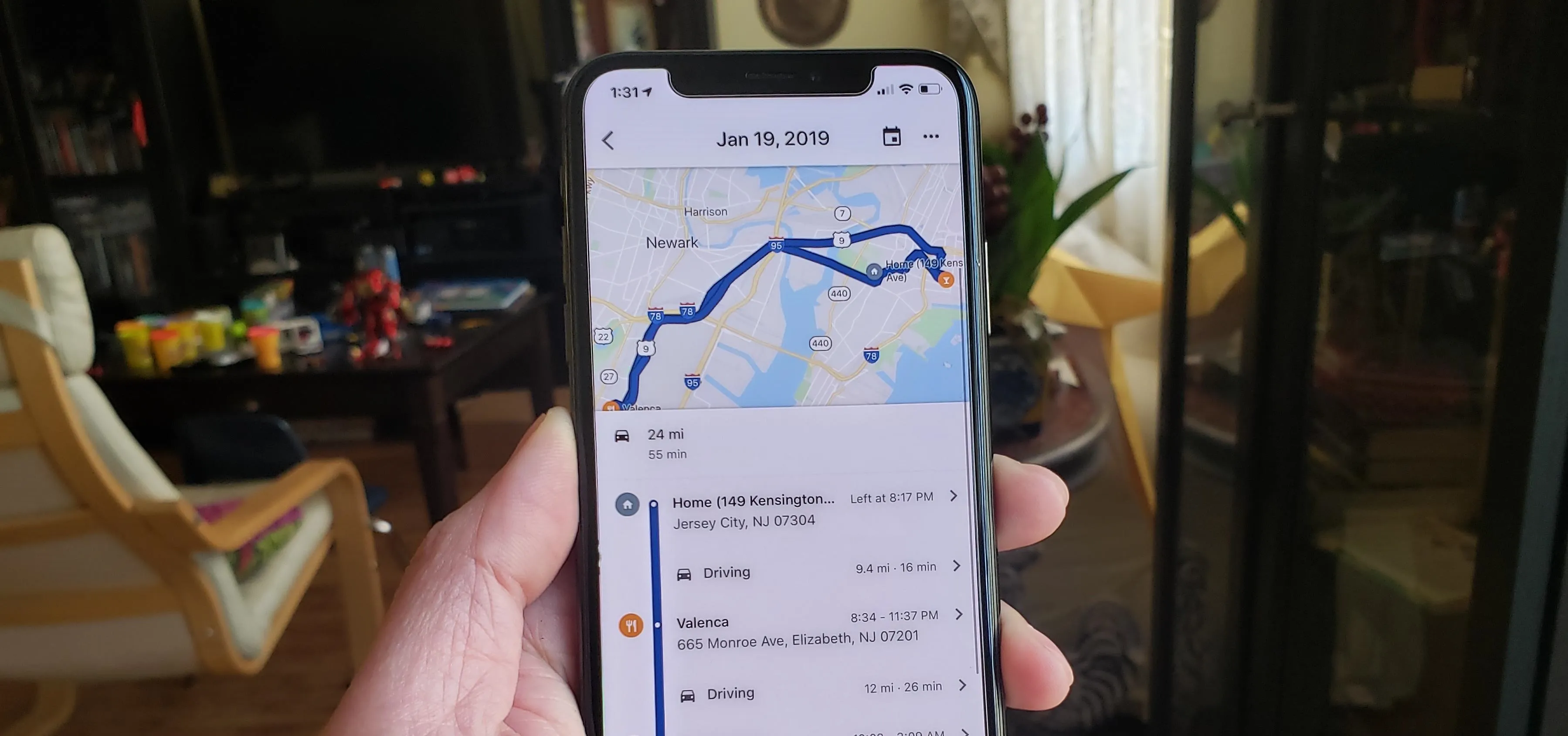
How to Hack Google